Intitle Index Of Google Hacks Ebook Reader
Smart Drug Dictionary: Index of Nootropic and Cognitive Enhancing Substances - Kindle edition by Donovan Roebuck. Free Download Mp3 Ran Dekat Di Hati Stafaband. Download it once and read it on your Kindle device.
As most of you want to learn hacking tricks (ethical) so in this post I am providing you the Best Hacking tricks PDF for free. In this download you will get the compilation of Best hacking tricks and eBooks that are free to download.

I have made your task of becoming a Pro Hacker easy as in order to learn ethical hacking you have to search eBooks and PDF on internet one by one so I have compiled them in one folder so that you can have all these hacking eBooks and hacking tricks PDF with a single click. I have tried to include all the hacking tips and tricks related to internet, PC, Mobile, Server’s many more The list of some of the Hacking Tricks and Tips compiled in this download are: • PC tricks • cmd tricks • windows tricks • networks tricks • Phreaking • server hijacking • server attacks • Client to prior attacks • Router tricks • Mobile tricks • WiFi pin hijacking and lots more to make you a pro hacker You can also download this collection to know how Hackers hack and gain some knowledge to protect your data and privacy. You will get lot of exposure towards hacking if you read this entire collection. Note:- These hacking eBooks and PDF are only for the ethical knowledge purpose and must not be used for illegal purposes. You can download the Hacking tricks PDF compilation by click above. Hope these books will came handing and be useful to learn some ethical hacking tricks at home by enhancing your skills from these hacking eBooks.
The list of all books are Best one and will be useful for you. Don’t forget to share this article with your friends and help them learn some cool hacking tricks as well. If you have any thing to ask then feel free to comment below and get your query cleared.!!
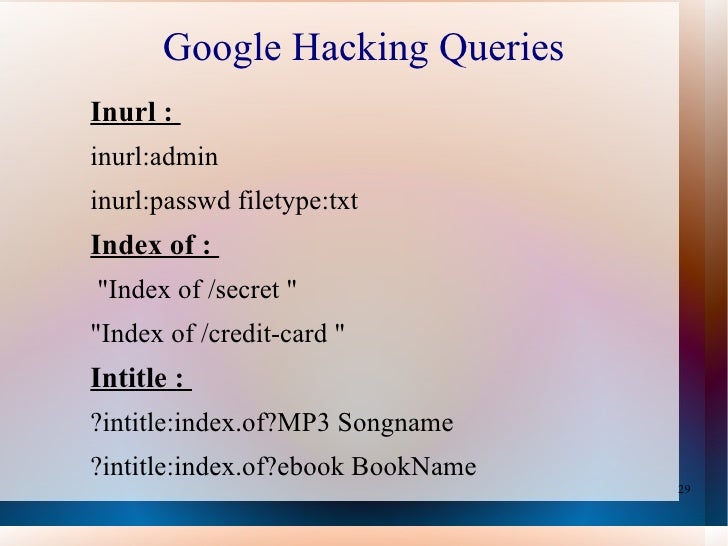
This book helps people find sensitive information on the Web. Google is one of the 5 most popular sites on the internet with more than 380 million unique users per month (Nielsen/NetRatings 8/05). But, Google’s search capabilities are so powerful, they sometimes discover content that no one ever intended to be publicly available on the Web including: social security numbers, credit card numbers, trade secrets, and federally classified documents. Google Hacking for Penetration Testers Volume 2 shows the art of manipulating Google used by security professionals and system administrators to find this sensitive information and “self-police their own organizations.
Readers will learn how Google Maps and Google Earth provide pinpoint military accuracy, see how bad guys can manipulate Google to create super worms, and see how they can 'mash up' Google with MySpace, LinkedIn, and more for passive reconaissance. • Learn Google Searching Basics Explore Google’s Web-based Interface, build Google queries, and work with Google URLs. • Use Advanced Operators to Perform Advanced Queries Combine advanced operators and learn about colliding operators and bad search-fu. • Learn the Ways of the Google Hacker See how to use caches for anonymity and review directory listings and traversal techniques.
• Review Document Grinding and Database Digging See the ways to use Google to locate documents and then search within the documents to locate information. • Understand Google’s Part in an Information Collection Framework Learn the principles of automating searches and the applications of data mining. • Locate Exploits and Finding Targets Locate exploit code and then vulnerable targets. • See Ten Simple Security Searches Learn a few searches that give good results just about every time and are good for a security assessment. • Track Down Web Servers Locate and profile web servers, login portals, network hardware and utilities.
• See How Bad Guys Troll for Data Find ways to search for usernames, passwords, credit card numbers, social security numbers, and other juicy information. • Hack Google Services Learn more about the AJAX Search API, Calendar, Blogger, Blog Search, and more. Syngress is committed to publishing high-quality books for IT Professionals and delivering those books in media and formats that fit the demands of our customers. We are also committed to extending the utility of the book you purchase via additional materials available from our Web site. SOLUTIONS WEB SITE To register your book, visit www.syngress.com/solutions. Once registered, you can access our solutions@syngress.com Web pages. There you will find an assortment of value-added features such as..
At syngress.com features overstocked, out-of-print, or slightly hurt books at significant savings. SITE LICENSING Syngress has a well-established program for site licensing our e-books onto servers in corporations, educational institutions, and large organizations. Contact us at sales@ syngress.com for more information.
CUSTOM PUBLISHING Many organizations welcome the ability to combine parts of multiple Syngress books, as well as their own content, into a single volume for their own internal.. Johnny Long is a Christian by grace, a professional hacker by trade, a pirate by blood, a ninja in training, a security researcher and author.
He can be found lurking at his website (He is the founder of Hackers For Charity(an organization that provides hackers with job experience while leveraging their skills for charities that need those skills. Bill Gardner is an Assistant Professor at Marshall University, where he teaches information security and foundational technology courses in the Department of Integrated Science and Technology. He is also President and Principal Security Consultant at BlackRock Consulting. In addition, Bill is Vice President and Information Security Chair at the Appalachian Institute of Digital Evidence.
AIDE is a non-profit organization that provides research and training for digital evidence professionals including attorneys, judges, law enforcement officers and information security practitioners in the private sector. Prior to joining the faculty at Marshall, Bill co-founded the Hack3rCon convention, and co-founded 304blogs, and he continues to serve as Vice President of 304Geeks. In addition, Bill is a founding member of the Security Awareness Training Framework, which will be a prime target audience for this book. Justin Brown (@spridel11) is an Information Assurance Analyst at a large financial institution. Previously, Justin worked for as a consultant specializing in Open Source Intelligence.
Through Google Hacking and dorks Justin has uncovered numerous troves of information leaks regarding his clients. Justin can usually be found at conferences volunteering with Hackers for Charity.